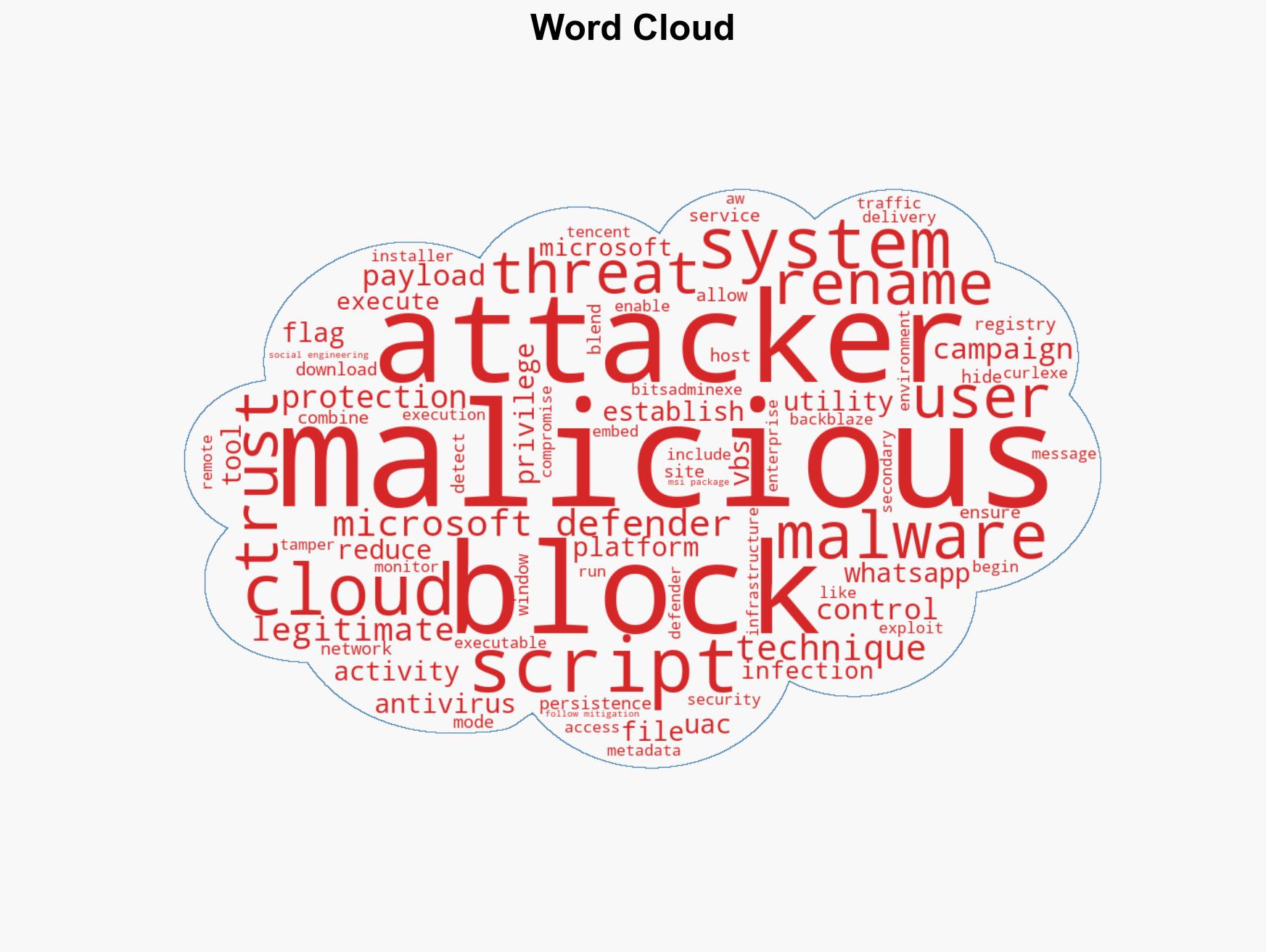
WhatsApp-Driven Malware Campaign Deploys VBS Scripts and MSI Backdoors for Remote Access
Published on: 2026-03-31
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: WhatsApp malware campaign delivers VBS payloads and MSI backdoors
1. BLUF (Bottom Line Up Front)
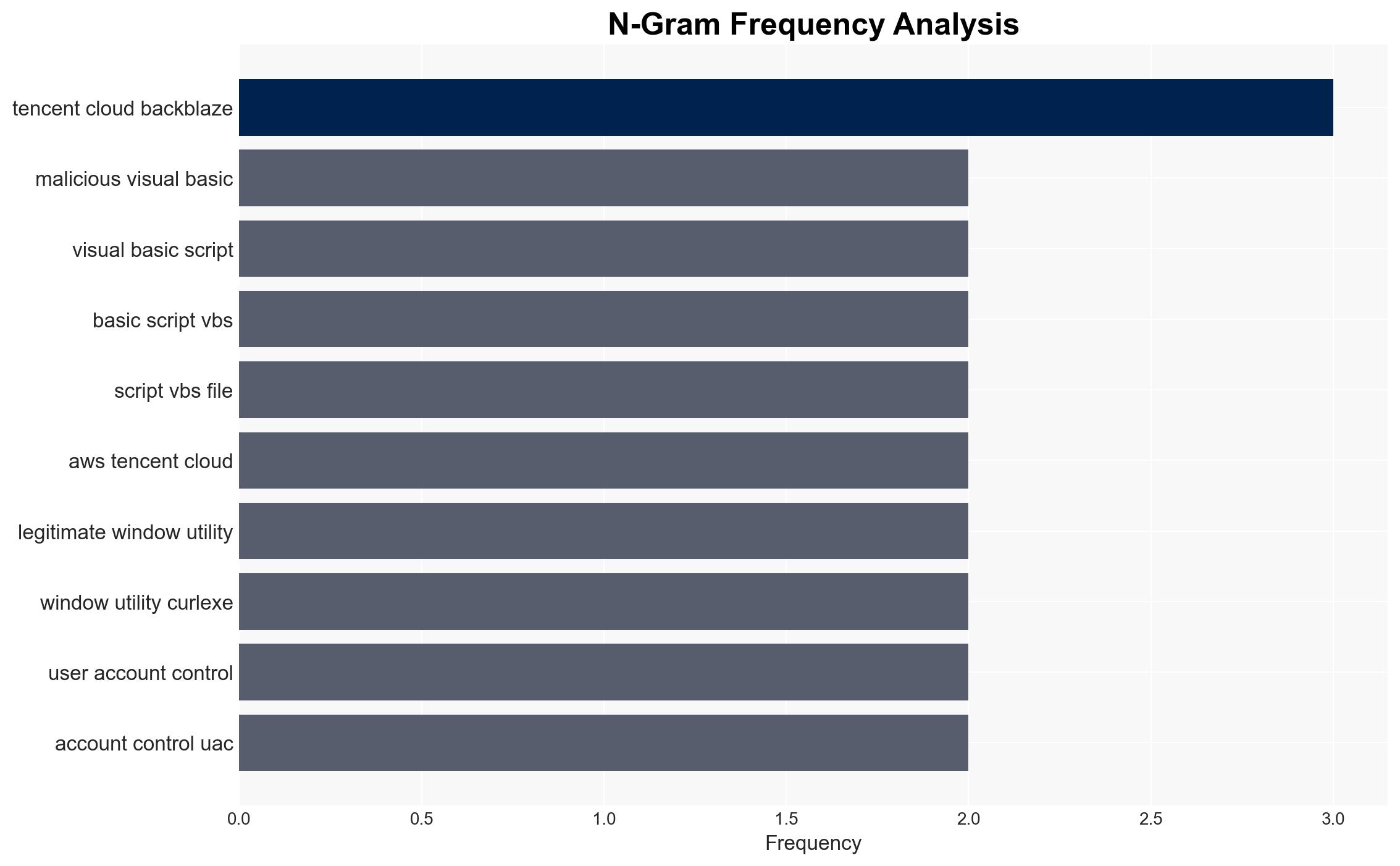
The observed malware campaign leverages WhatsApp for delivery of malicious VBS files, establishing persistence and remote access through sophisticated techniques. The campaign primarily affects users trusting familiar platforms, with moderate confidence in the assessment due to reliance on open-source data and potential for deception. The most likely hypothesis is that the campaign aims to exploit cloud services for stealthy operations.
2. Competing Hypotheses
- Hypothesis A: The campaign is primarily designed to exploit user trust in WhatsApp and cloud services to establish long-term persistence and control over targeted systems. This is supported by the use of social engineering and legitimate tools to evade detection. Key uncertainties include the ultimate objectives and potential state sponsorship.
- Hypothesis B: The campaign is a financially motivated operation focused on data exfiltration and ransomware deployment. This is less supported due to the lack of direct evidence of financial gain activities in the observed tactics.
- Assessment: Hypothesis A is currently better supported due to the sophistication of the techniques and the focus on persistence and stealth, which are indicative of strategic, possibly state-sponsored objectives. Indicators such as changes in target profiles or new payloads could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The threat actor has advanced capabilities; the use of WhatsApp is intentional for trust exploitation; cloud services are chosen for their perceived legitimacy.
- Information Gaps: Lack of information on the threat actor’s identity, specific targets, and end goals; absence of data on potential state sponsorship.
- Bias & Deception Risks: Potential for cognitive bias in attributing sophistication to state actors; risk of deception through false flag operations or misleading tactics.
4. Implications and Strategic Risks
This campaign could evolve to target more critical infrastructure sectors, leveraging its stealth capabilities to infiltrate sensitive networks. The use of trusted platforms poses a risk of widespread exploitation.
- Political / Geopolitical: Potential escalation if linked to state actors, affecting international relations and cybersecurity policies.
- Security / Counter-Terrorism: Increased threat to national security infrastructure, requiring enhanced monitoring and response capabilities.
- Cyber / Information Space: Challenges in attribution and defense due to use of legitimate tools and cloud services; potential for misinformation campaigns.
- Economic / Social: Possible economic impact from disruptions in targeted sectors; erosion of trust in digital communication platforms.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of WhatsApp and cloud service traffic; deploy advanced threat detection solutions focusing on metadata discrepancies.
- Medium-Term Posture (1–12 months): Develop partnerships with cloud service providers for threat intelligence sharing; invest in user education on social engineering risks.
- Scenario Outlook:
- Best: Effective mitigation leads to reduced campaign impact; increased collaboration with tech companies.
- Worst: Campaign evolves to target critical infrastructure, causing significant disruptions.
- Most-Likely: Continued low-level exploitation with gradual improvements in detection and response capabilities.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, malware, social engineering, cloud services, state-sponsored threats, information security, digital trust
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us