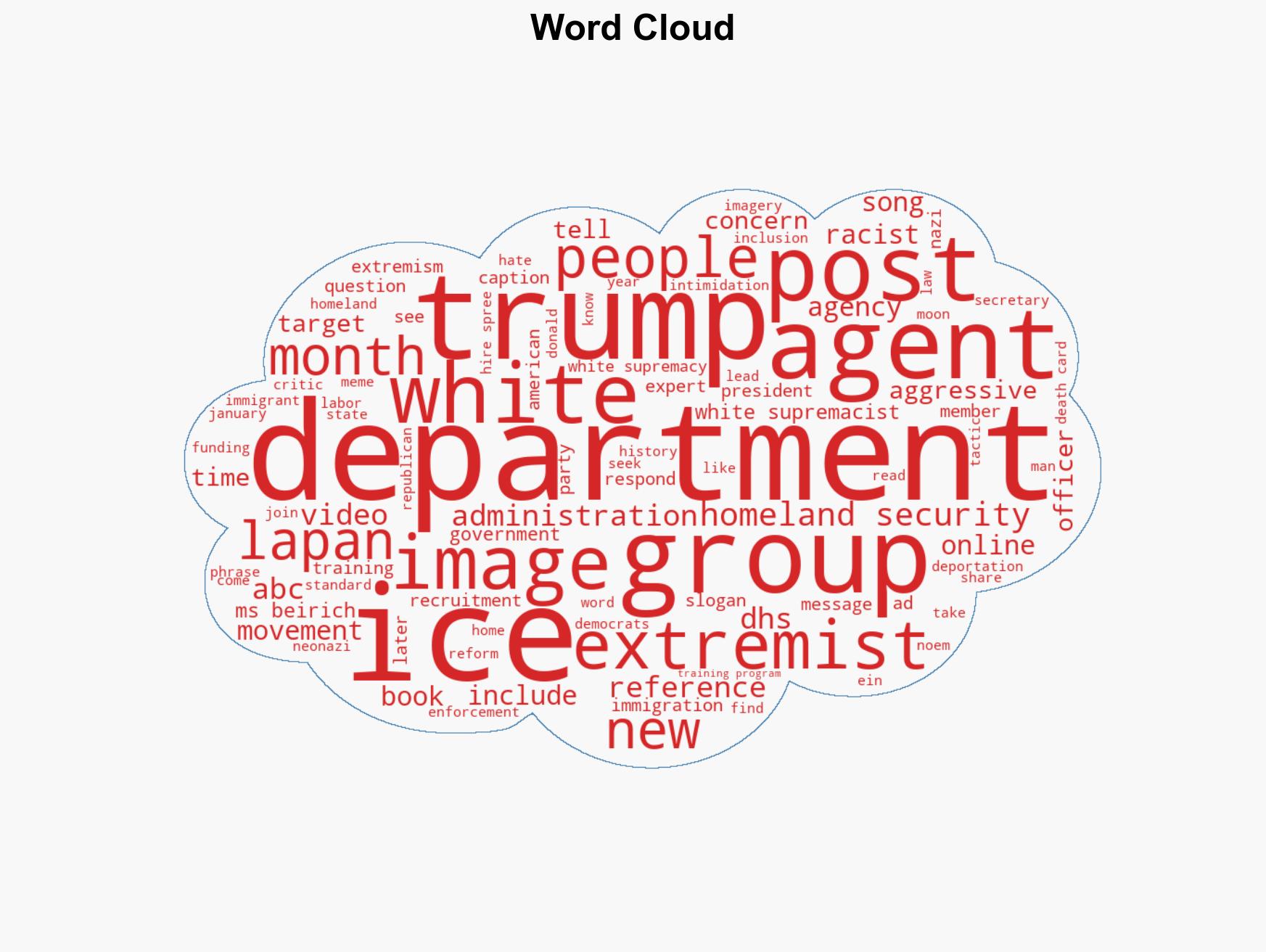
White Supremacist Imagery Emerges in Recruitment Campaign for ICE Agents
Published on: 2026-03-21
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: How ‘white supremacist’ material was used to hire an army of ICE agents
1. BLUF (Bottom Line Up Front)
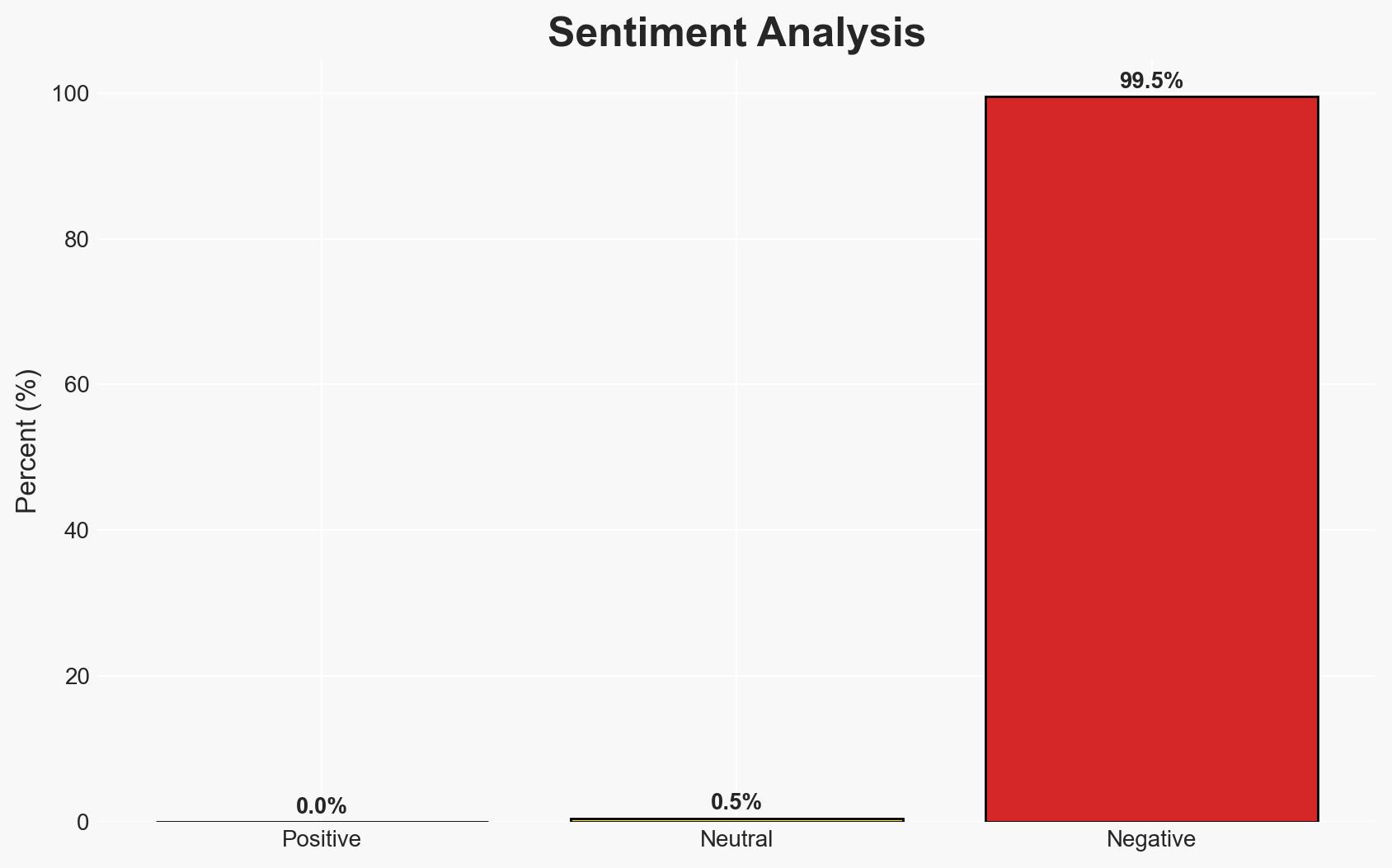
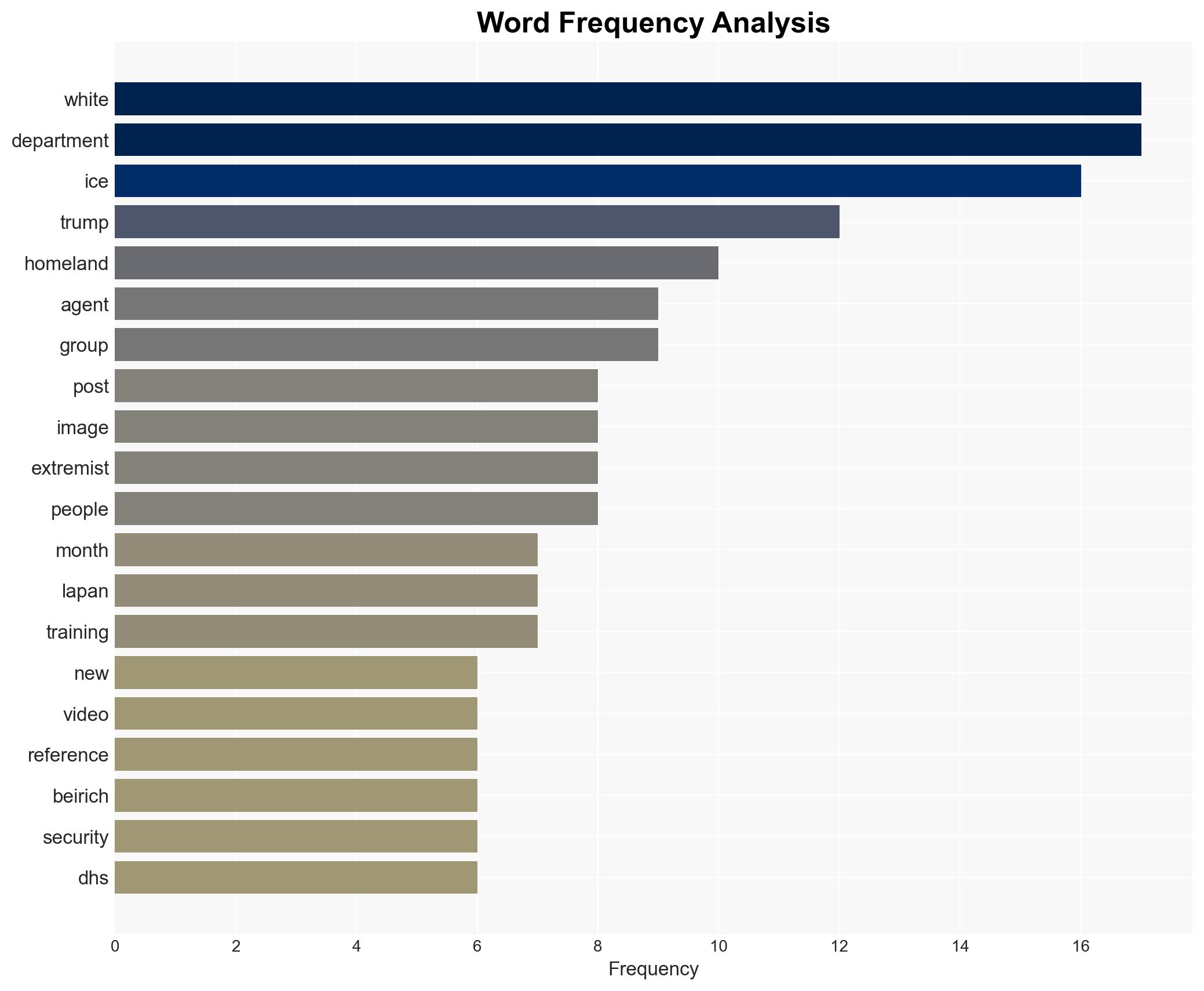
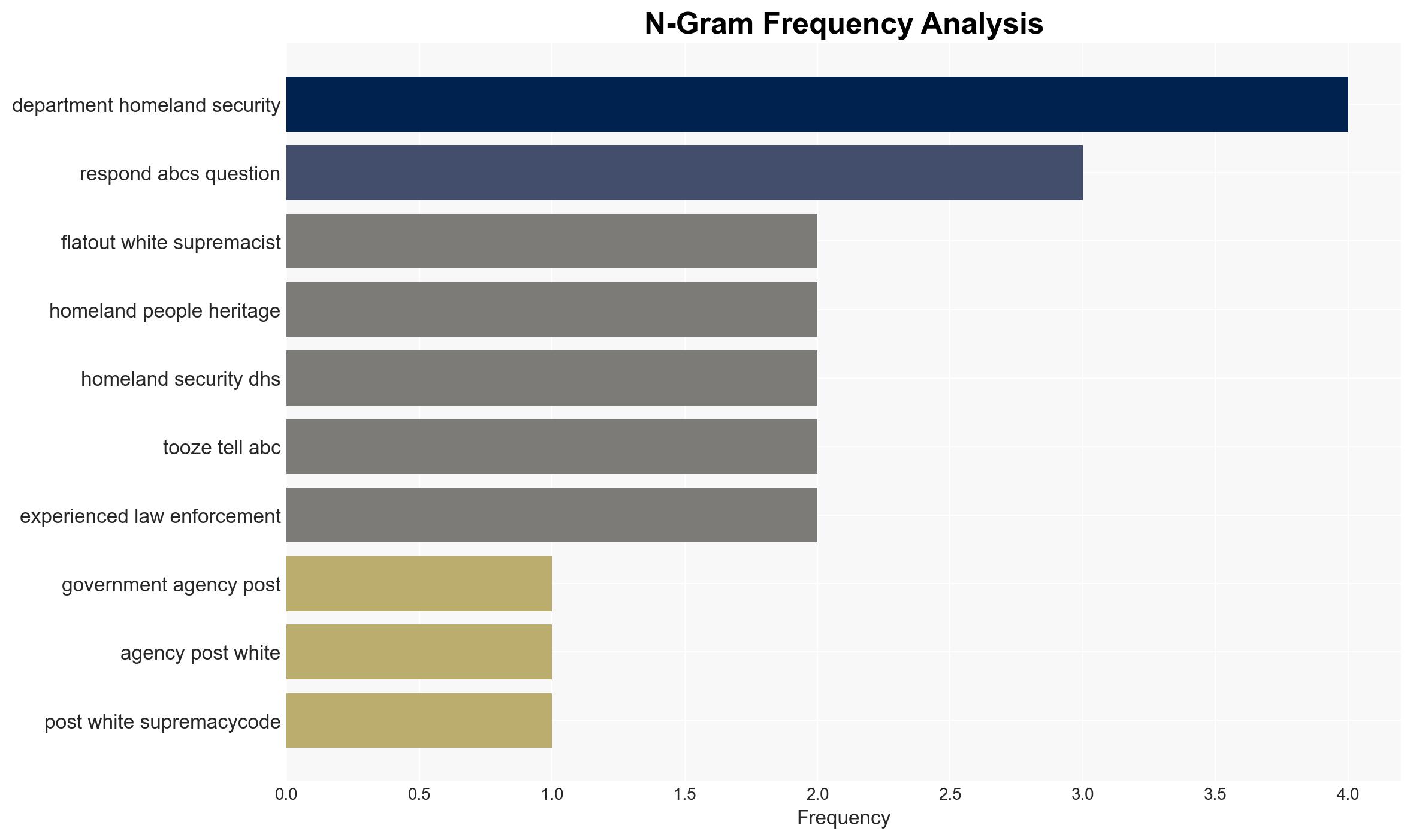
The use of white supremacist-coded imagery in US government social media during a hiring spree for ICE agents suggests a deliberate attempt to signal to extremist groups. This development has potential implications for national security and public trust. The most likely hypothesis is that these actions were intentional, with moderate confidence in this assessment.
2. Competing Hypotheses
- Hypothesis A: The inclusion of white supremacist imagery was a deliberate strategy to appeal to extremist groups and bolster recruitment efforts. This is supported by the timing, the nature of the content, and expert opinions. However, there is uncertainty regarding the extent of official endorsement or oversight.
- Hypothesis B: The imagery was included accidentally due to a lack of oversight or understanding of extremist symbols by social media teams. This hypothesis is less supported due to the repeated nature of the incidents and expert analysis suggesting intentionality.
- Assessment: Hypothesis A is currently better supported due to the pattern of behavior and expert testimony. Indicators such as further similar incidents or internal communications could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The social media content was created with a specific target audience in mind; the imagery is recognized by extremist groups as a signal; there is a coordinated strategy behind the content.
- Information Gaps: Internal communications or directives regarding the social media strategy; the decision-making process behind content approval; the extent of awareness among higher-level officials.
- Bias & Deception Risks: Potential confirmation bias in interpreting the imagery; source bias from experts with specific agendas; possible deliberate manipulation by actors within the agencies.
4. Implications and Strategic Risks
This development could exacerbate divisions within the US, influence extremist recruitment, and affect international perceptions of US governance.
- Political / Geopolitical: Potential erosion of public trust in government institutions and increased scrutiny from international allies.
- Security / Counter-Terrorism: Increased risk of radicalization and domestic terrorism as extremist groups feel validated.
- Cyber / Information Space: Potential for increased propaganda and misinformation campaigns leveraging these signals.
- Economic / Social: Possible impact on social cohesion and economic stability due to heightened tensions and public unrest.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct an internal review of social media content approval processes; increase monitoring of extremist online activities.
- Medium-Term Posture (1–12 months): Develop partnerships with civil society to counter extremist narratives; enhance training for government communication teams on extremist symbols.
- Scenario Outlook:
- Best: Quick corrective actions restore public trust and deter extremist recruitment.
- Worst: Continued use of such imagery leads to increased domestic terrorism and international isolation.
- Most-Likely: Gradual improvements in oversight reduce incidents, but public skepticism remains.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
national security threats, extremism, national security, immigration policy, social media strategy, public trust, domestic terrorism, government communications
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Expose and correct potential biases in assessments through red-teaming and structured challenge.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us