Why no business is safe from state-sponsored cyber attacks – TechRadar
Published on: 2025-04-03
Intelligence Report: Why no business is safe from state-sponsored cyber attacks – TechRadar
1. BLUF (Bottom Line Up Front)
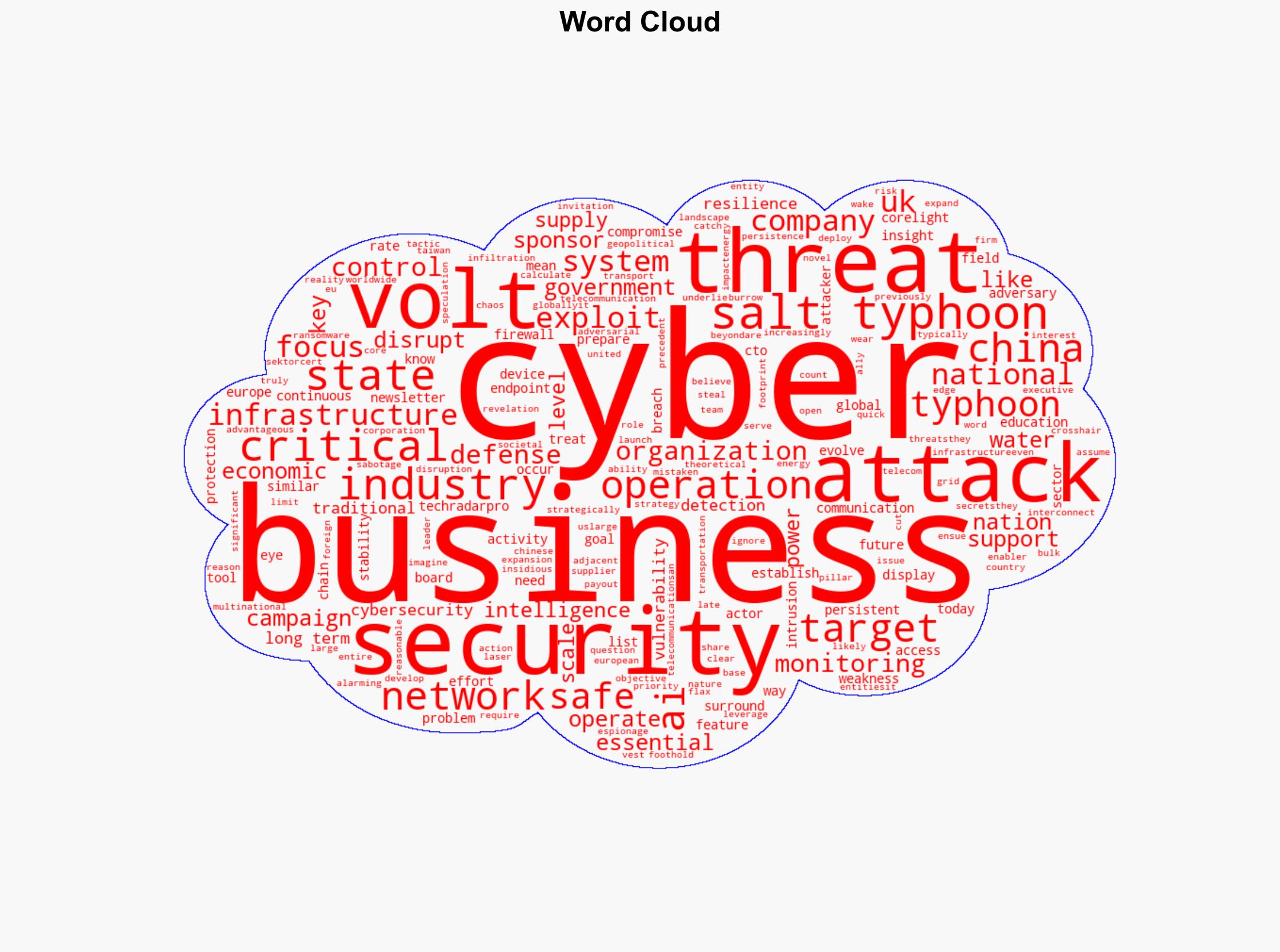
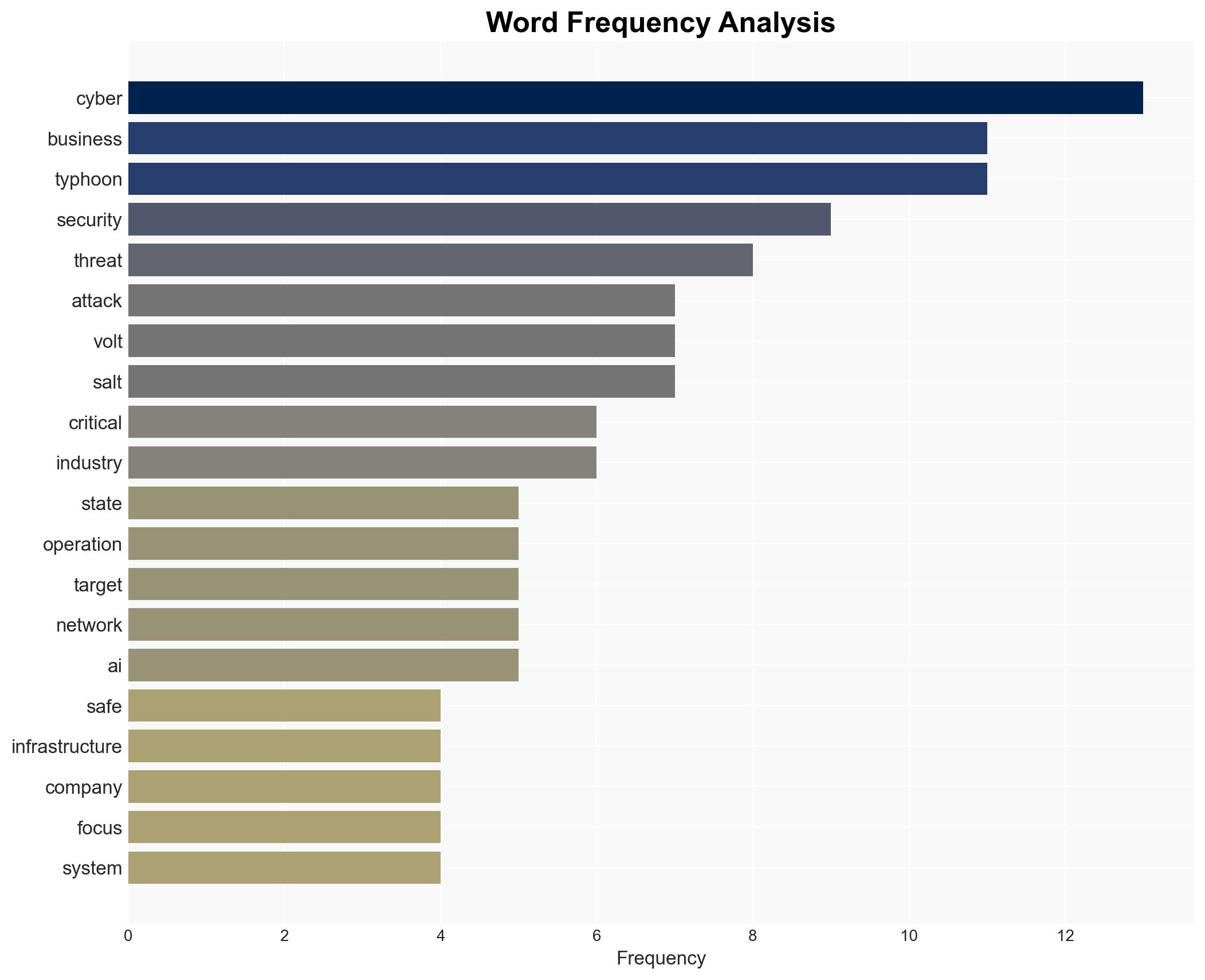
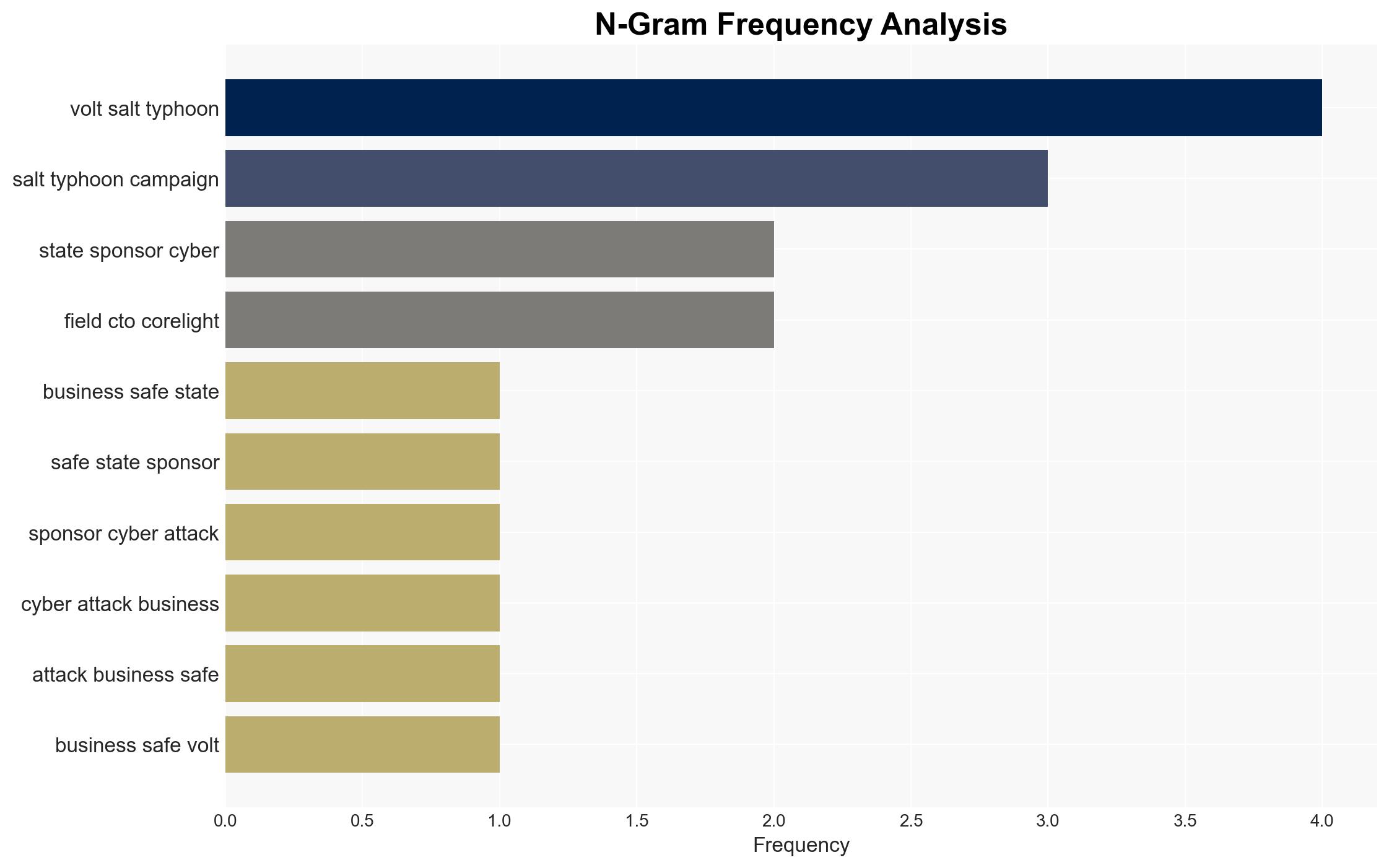
State-sponsored cyber attacks, particularly from China, pose a significant threat to businesses globally. Campaigns such as Volt Typhoon and Salt Typhoon highlight the evolving threat landscape, with a focus on establishing long-term infiltration in critical infrastructure sectors. Businesses, especially those in energy, telecommunications, and transportation, must prioritize cybersecurity at the board level to mitigate these threats.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
Recent revelations about China’s cyber operations, specifically Volt Typhoon and Salt Typhoon, indicate a strategic focus on long-term infiltration rather than immediate financial gain. These operations target critical infrastructure in the United States and potentially extend to allies like the UK and Europe. The campaigns aim to establish persistent access to key systems, which could be exploited for geopolitical leverage. The use of AI in these operations enhances their capability to outpace traditional corporate defenses.
3. Implications and Strategic Risks
The implications of these cyber campaigns are profound, with potential risks to national security, regional stability, and economic interests. The targeted sectors—energy, telecommunications, and transportation—are pillars of economic and societal stability. Disruption in these areas could lead to significant chaos and weaken national defenses. The use of AI in cyber operations suggests an evolving threat that traditional security measures may not adequately address.
4. Recommendations and Outlook
Recommendations:
- Enhance cybersecurity measures at the board level, treating it as a core risk management issue.
- Invest in AI-driven defense mechanisms to counter AI-powered cyber threats.
- Strengthen international collaboration for intelligence sharing and coordinated responses to cyber threats.
Outlook:
In the best-case scenario, businesses will adapt to the evolving threat landscape by integrating advanced cybersecurity technologies and fostering international cooperation. In the worst-case scenario, failure to address these threats could lead to widespread disruption of critical infrastructure. The most likely outcome is a continued escalation of cyber threats, prompting gradual improvements in cybersecurity practices across industries.
5. Key Individuals and Entities
The report references significant cyber campaigns such as Volt Typhoon and Salt Typhoon, which are linked to Chinese state-sponsored activities. These campaigns are indicative of a broader strategy to target critical infrastructure globally.