Wynn Resorts relies on hackers’ claims of deleted employee data following cyberattack
Published on: 2026-02-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Wynn Resorts takes attacker’s word for it that stolen staff data was deleted
1. BLUF (Bottom Line Up Front)
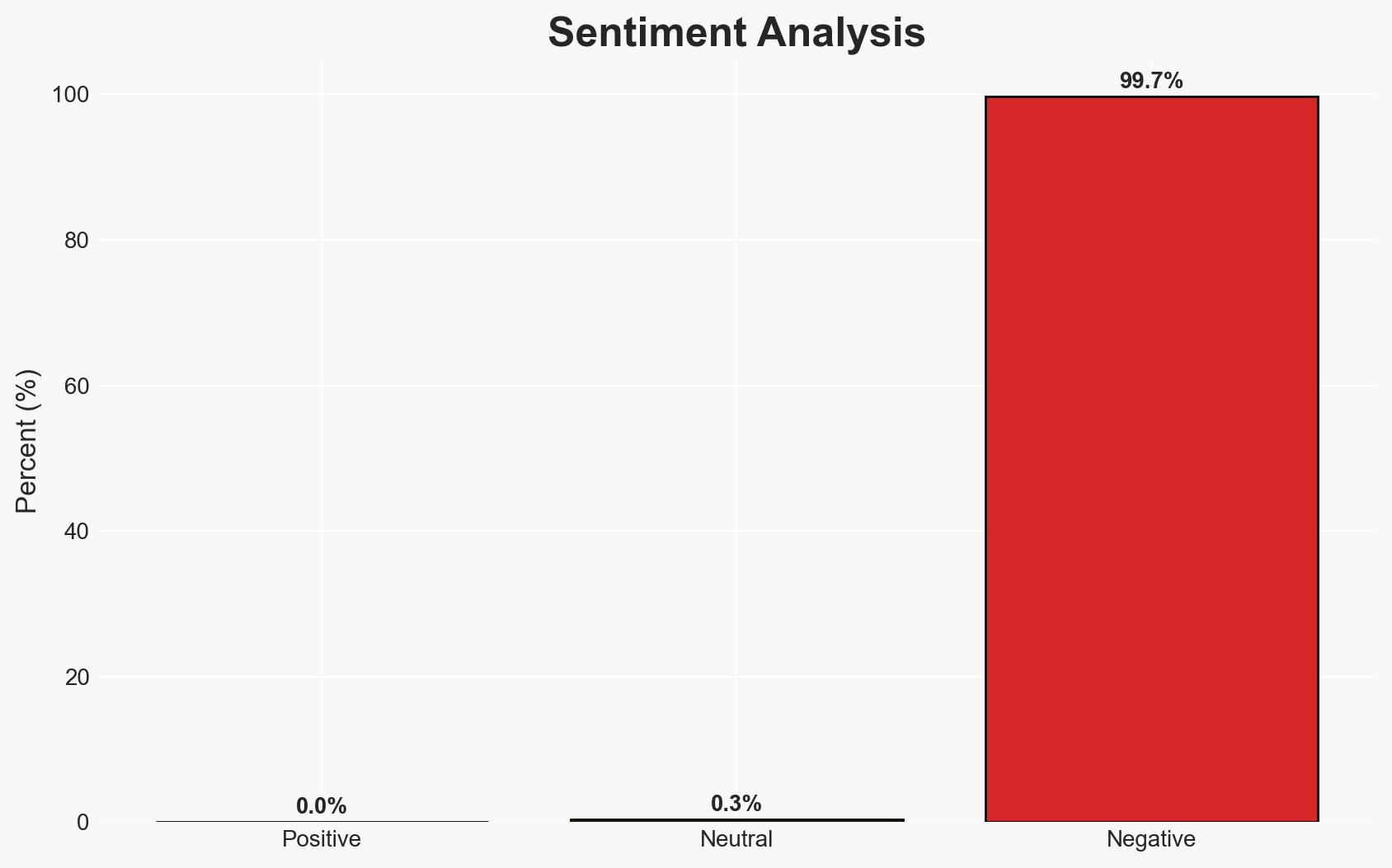
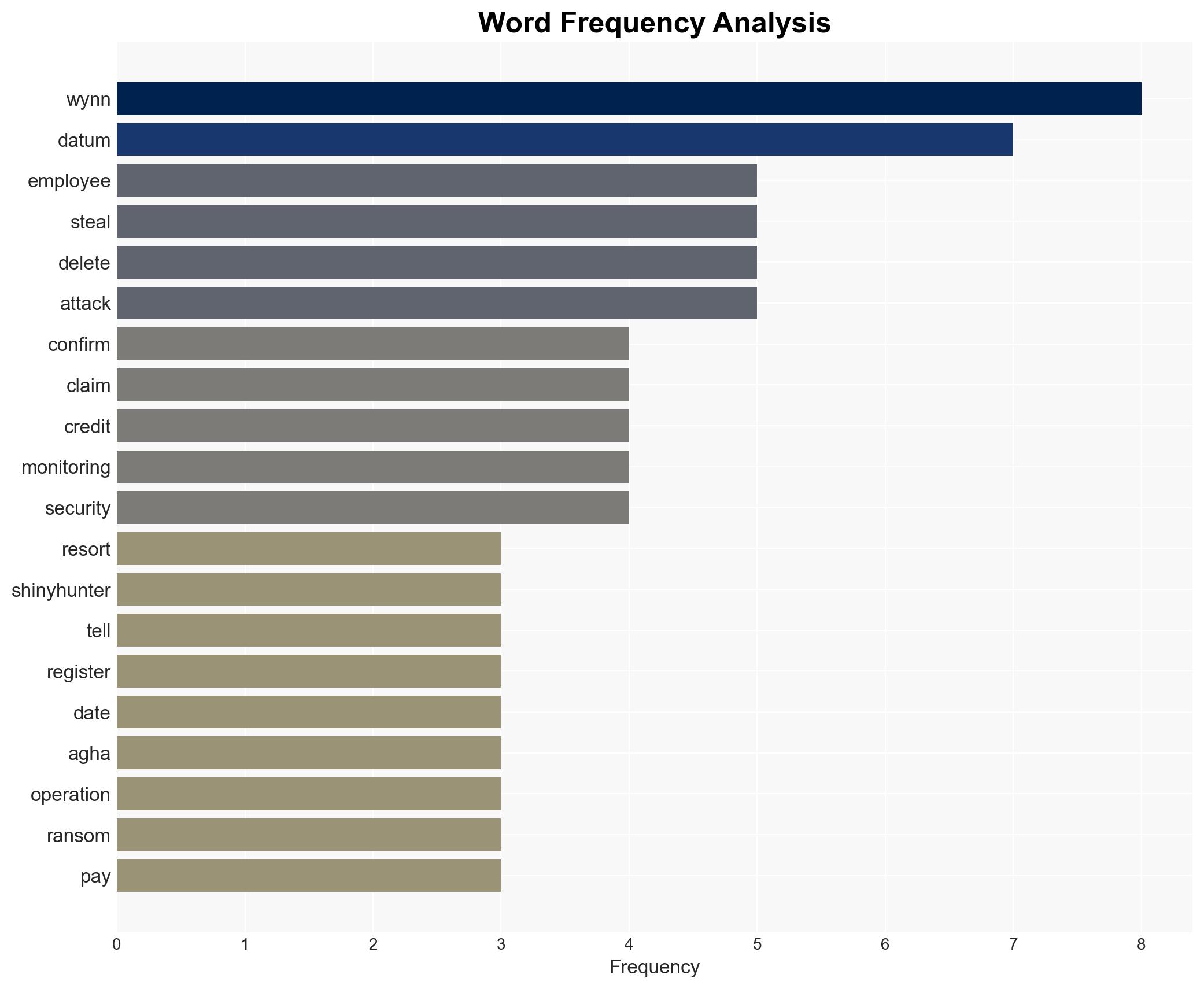
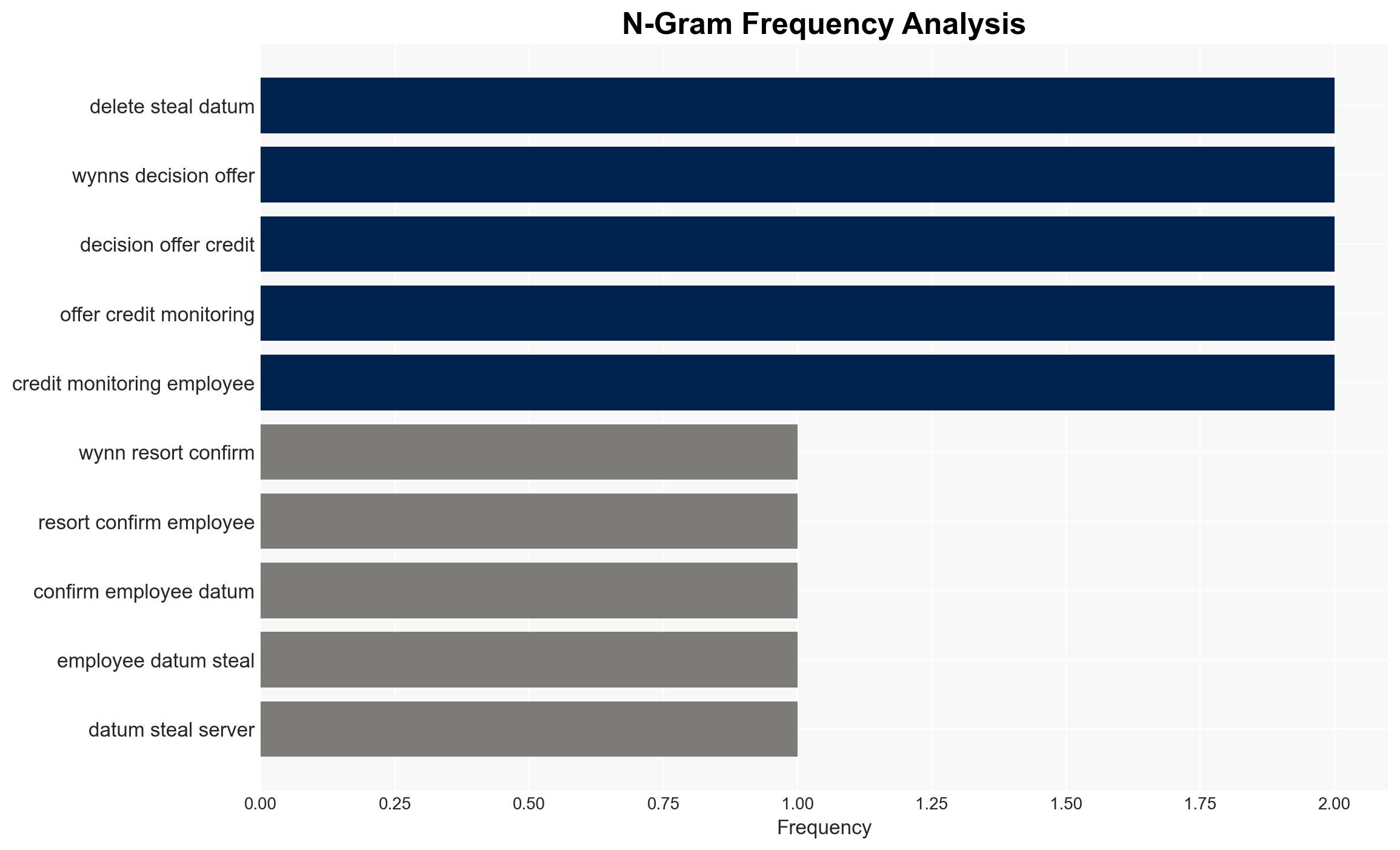
Wynn Resorts has opted to trust the assurance of the cybercrime group ShinyHunters that stolen employee data has been deleted, despite the inherent risks of such trust. This decision reflects a potential ransom payment, though unconfirmed, and highlights vulnerabilities in corporate cyber response strategies. The situation primarily affects Wynn Resorts’ employees and could have broader implications for corporate cybersecurity practices. Overall confidence in this assessment is moderate due to significant information gaps.
2. Competing Hypotheses
- Hypothesis A: Wynn Resorts paid a ransom to ShinyHunters, who then claimed to have deleted the stolen data. This is supported by the typical behavior of cybercriminals post-extortion and the provision of credit monitoring to employees. However, the lack of explicit confirmation from Wynn introduces uncertainty.
- Hypothesis B: Wynn Resorts did not pay a ransom, and the claim of data deletion is a strategic move by ShinyHunters to maintain credibility. The absence of evidence of data misuse supports this, but it contradicts typical extortion practices.
- Assessment: Hypothesis A is currently better supported due to the alignment with common cybercriminal behavior and the precautionary measures taken by Wynn. Key indicators that could shift this judgment include confirmation of ransom payment or evidence of data misuse.
3. Key Assumptions and Red Flags
- Assumptions: Wynn Resorts’ decision is based on a rational assessment of risk; ShinyHunters’ assurance of deletion is typical post-extortion behavior; the lack of data misuse indicates compliance by the attackers.
- Information Gaps: Confirmation of any ransom payment; details on the data’s current status; insights into ShinyHunters’ operational patterns.
- Bias & Deception Risks: Potential cognitive bias in assuming typical behavior of cybercriminals; source bias from relying on Wynn’s statements; deception risk from the cybercriminals’ assurance of deletion.
4. Implications and Strategic Risks
This development could influence corporate cybersecurity strategies and extortion negotiations, potentially encouraging similar trust-based resolutions. The broader dynamics of cybercrime and corporate vulnerability may be affected.
- Political / Geopolitical: Increased scrutiny on corporate cybersecurity practices may lead to regulatory changes.
- Security / Counter-Terrorism: No direct implications, but highlights vulnerabilities in corporate cyber defenses.
- Cyber / Information Space: May embolden cybercriminals to exploit trust-based resolutions, impacting the cyber threat landscape.
- Economic / Social: Potential reputational damage to Wynn Resorts, affecting employee trust and stakeholder confidence.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring for any signs of data misuse; engage with cybersecurity experts to verify data deletion claims.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity protocols; develop incident response strategies that do not rely on trust in cybercriminals.
- Scenario Outlook: Best: Data remains unused, and Wynn’s reputation is intact. Worst: Data is misused, leading to legal and reputational damage. Most-Likely: Data remains unused, but Wynn faces increased scrutiny and pressure to improve cybersecurity.
6. Key Individuals and Entities
- Wynn Resorts
- ShinyHunters
- Dray Agha, Senior Manager of Security Operations at Huntress
7. Thematic Tags
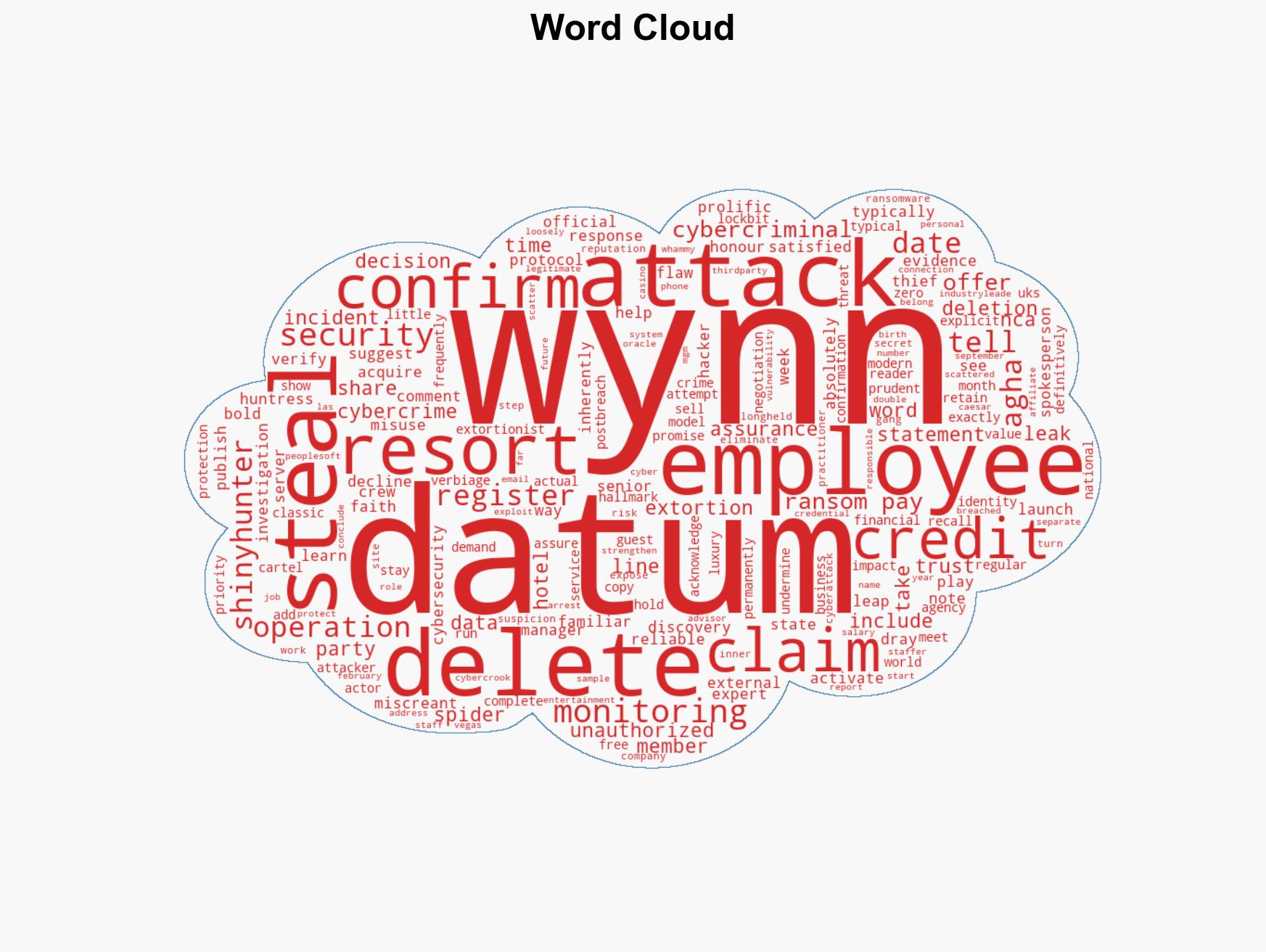
cybersecurity, data breach, extortion, corporate risk, cybercrime, employee data, incident response
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us