Zyxel issues security updates for critical RCE vulnerability in multiple router models affecting remote acces…
Published on: 2026-02-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Zyxel warns of critical RCE flaw affecting over a dozen routers
1. BLUF (Bottom Line Up Front)
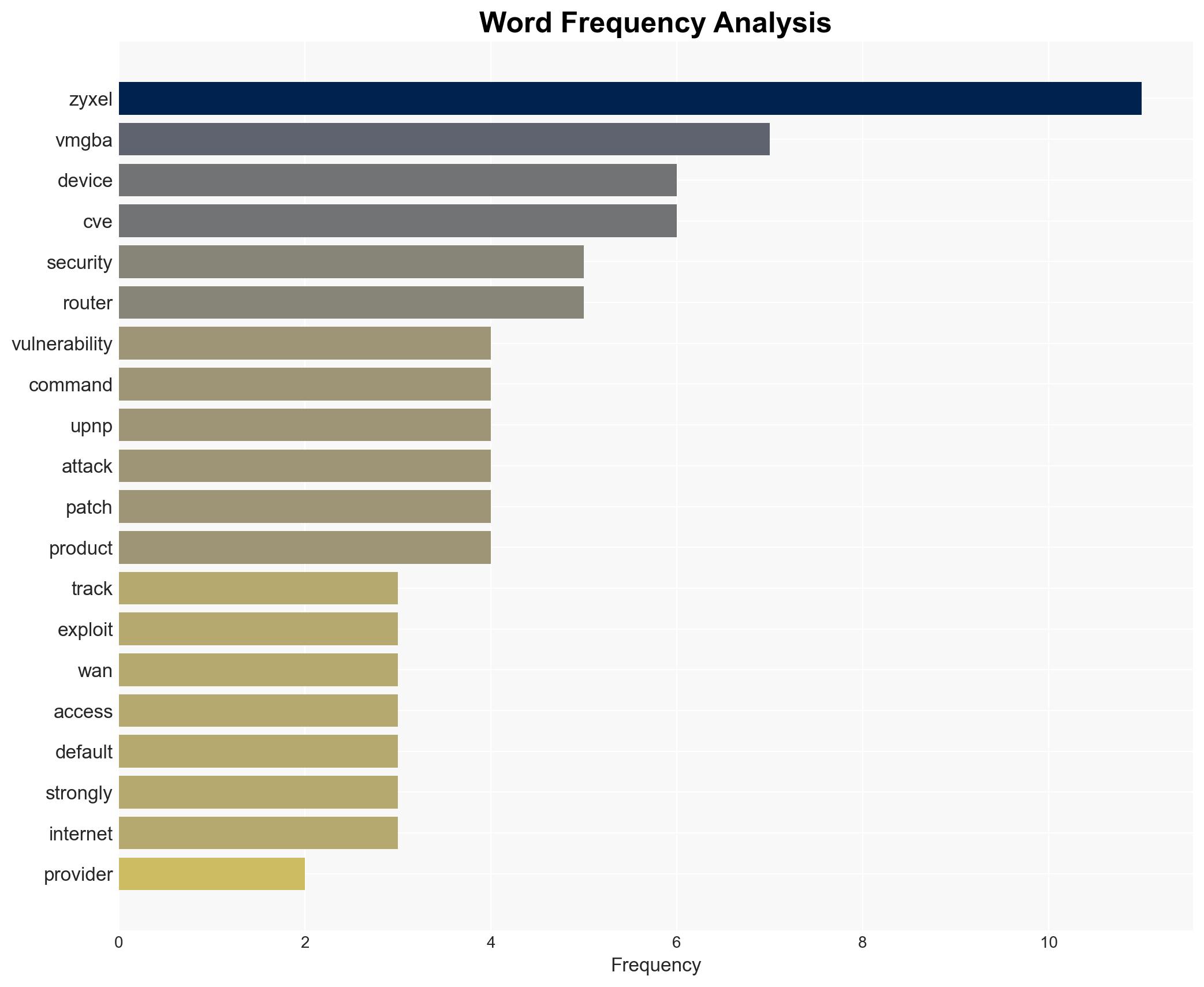
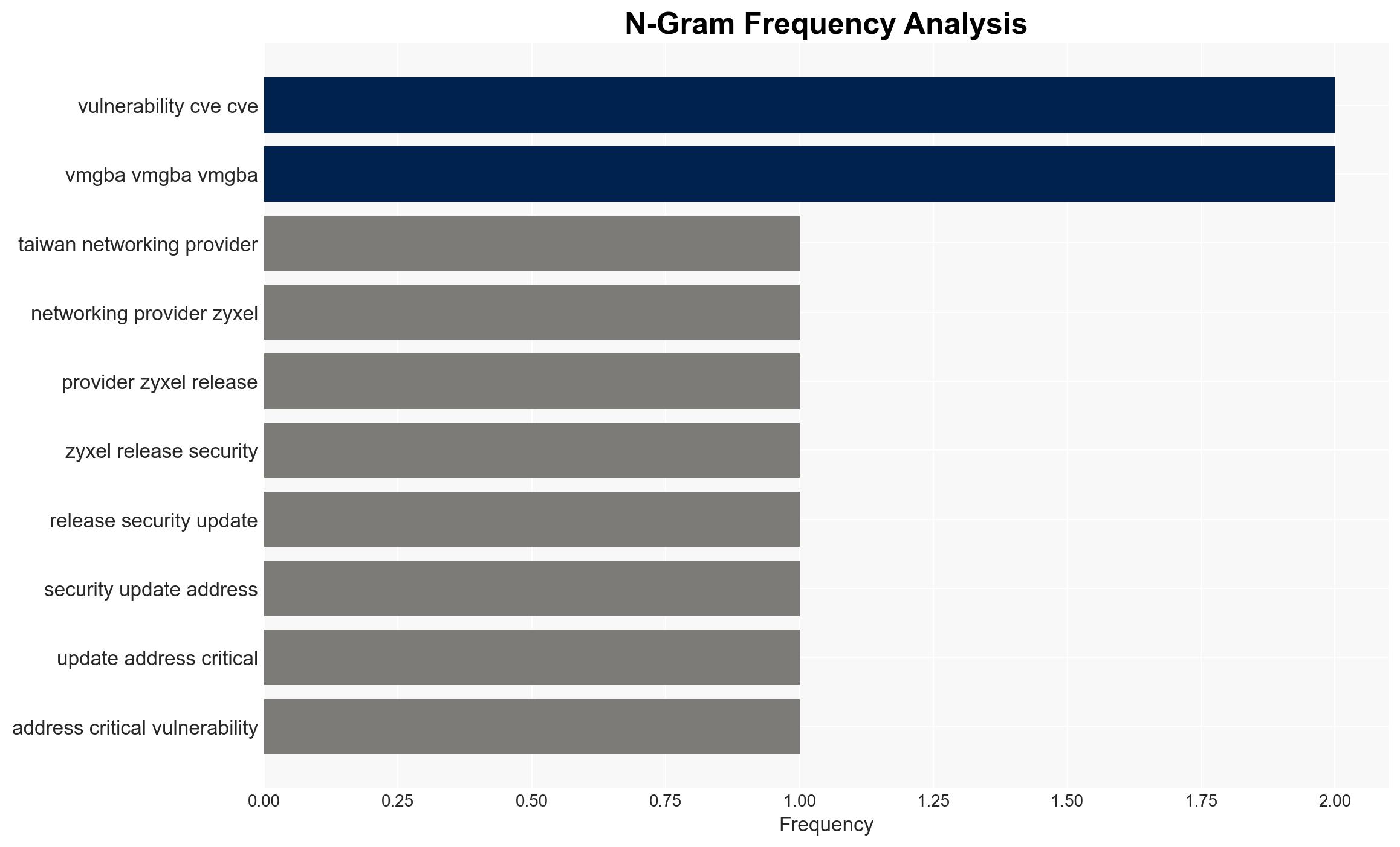
Zyxel has identified a critical remote command execution (RCE) vulnerability affecting over a dozen router models, potentially impacting up to 120,000 internet-exposed devices. The vulnerability requires specific conditions to be exploited, limiting its immediate threat. However, given the widespread use of Zyxel devices, there is a moderate confidence that this could pose significant security risks if not mitigated promptly.
2. Competing Hypotheses
- Hypothesis A: The vulnerability will have limited impact due to the default settings that disable WAN access, reducing the likelihood of exploitation. This is supported by Zyxel’s statement and the technical requirement for both UPnP and WAN access to be enabled.
- Hypothesis B: The vulnerability could be widely exploited due to the large number of devices in use and potential user misconfigurations enabling WAN access. This is supported by the number of internet-exposed devices and the history of Zyxel devices being targeted.
- Assessment: Hypothesis A is currently better supported due to the default security settings. However, changes in user behavior or targeted attacks could shift this assessment. Indicators such as increased reports of exploitation or changes in default settings would warrant reassessment.
3. Key Assumptions and Red Flags
- Assumptions: Users will apply the patches provided by Zyxel; WAN access remains disabled by default; attackers lack widespread capability to exploit the vulnerability en masse.
- Information Gaps: The exact number of devices with WAN access enabled; the speed and extent of patch deployment by users.
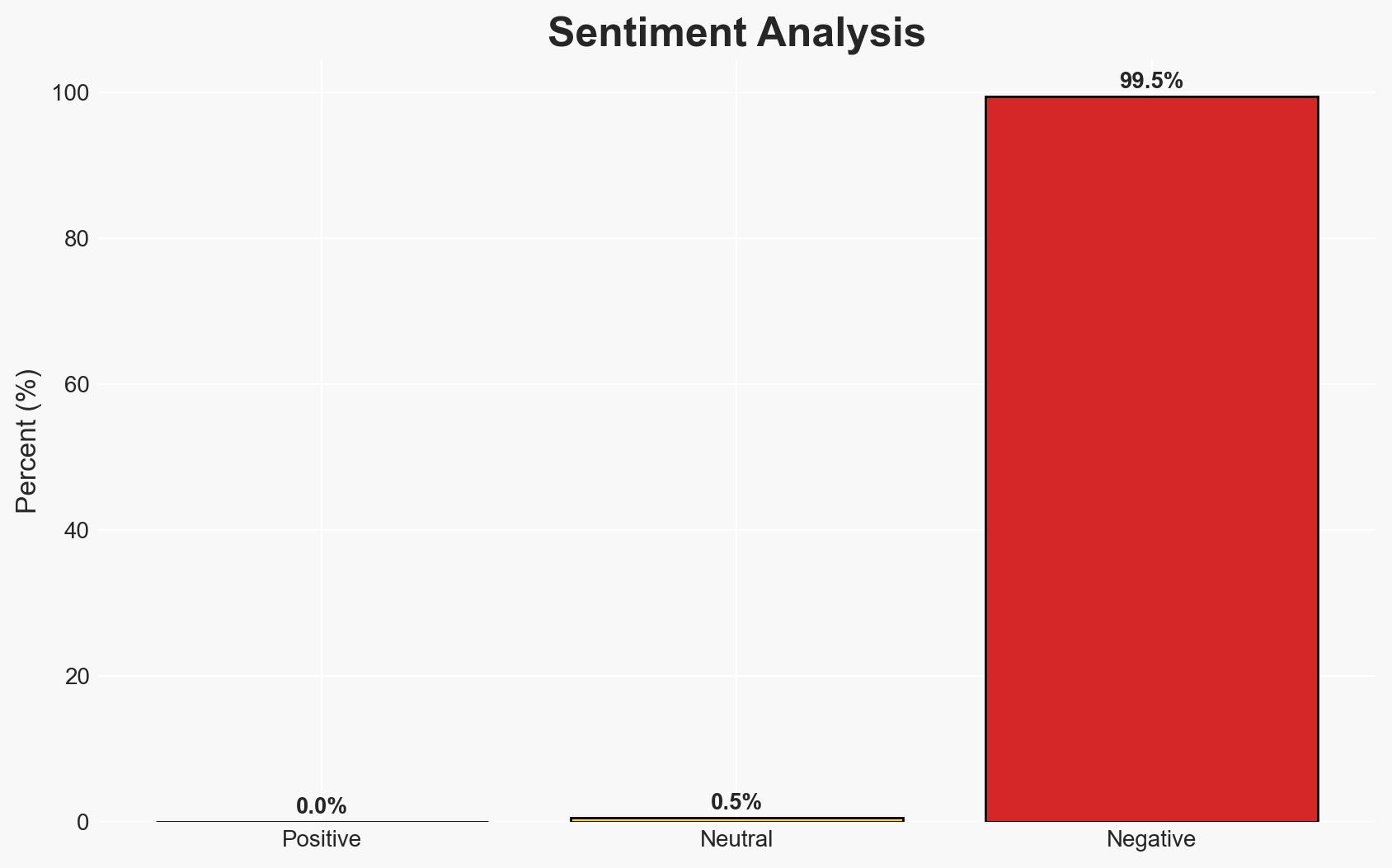
- Bias & Deception Risks: Potential underreporting of successful exploits; reliance on vendor-provided information which may downplay risks.
4. Implications and Strategic Risks
The vulnerability, if exploited, could lead to unauthorized access to networks, data breaches, and potential disruptions in service. The situation could evolve as attackers develop more sophisticated methods to exploit the vulnerability.
- Political / Geopolitical: Minimal direct impact, but potential for increased scrutiny on cybersecurity practices and international cooperation on cyber threats.
- Security / Counter-Terrorism: Increased risk of cyber-attacks on critical infrastructure using compromised routers as entry points.
- Cyber / Information Space: Potential for increased cyber espionage and data theft activities targeting vulnerable devices.
- Economic / Social: Financial losses for businesses relying on compromised devices; potential loss of consumer trust in Zyxel products.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage users to apply patches immediately; monitor for signs of exploitation; increase awareness campaigns about securing devices.
- Medium-Term Posture (1–12 months): Develop partnerships with ISPs to ensure secure configurations; enhance user education on device security; invest in research for better vulnerability detection.
- Scenario Outlook:
- Best: Rapid patch deployment and user compliance minimize exploitation risks.
- Worst: Widespread exploitation due to user negligence or targeted attacks.
- Most-Likely: Limited exploitation with isolated incidents due to effective patching and awareness efforts.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
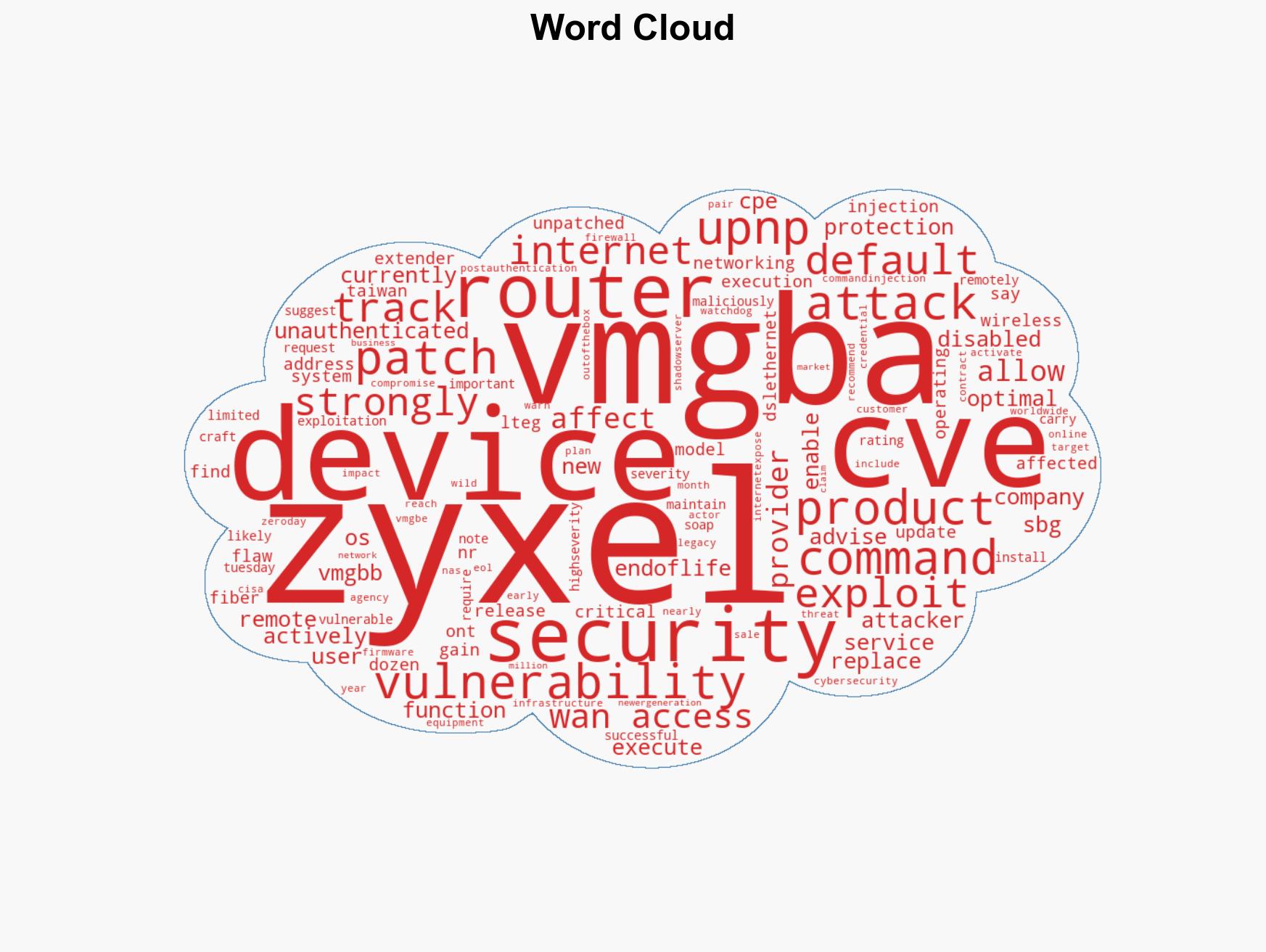
cybersecurity, vulnerability management, network security, remote command execution, internet of things, critical infrastructure, cyber threats
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us