CISA reveals new malware variant used on compromised Ivanti Connect Secure devices – Help Net Security
Published on: 2025-03-31
Intelligence Report: CISA reveals new malware variant used on compromised Ivanti Connect Secure devices – Help Net Security
1. BLUF (Bottom Line Up Front)
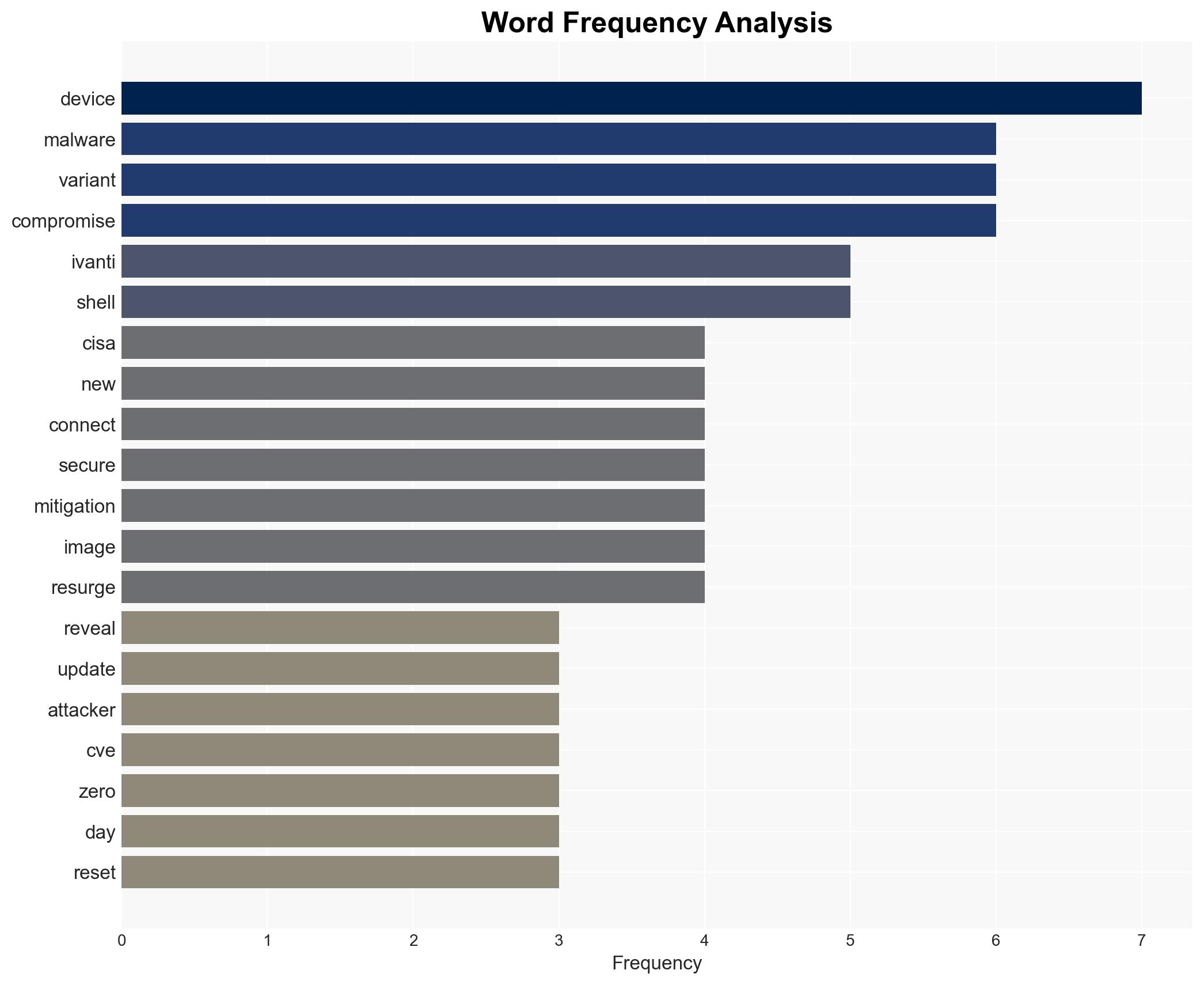
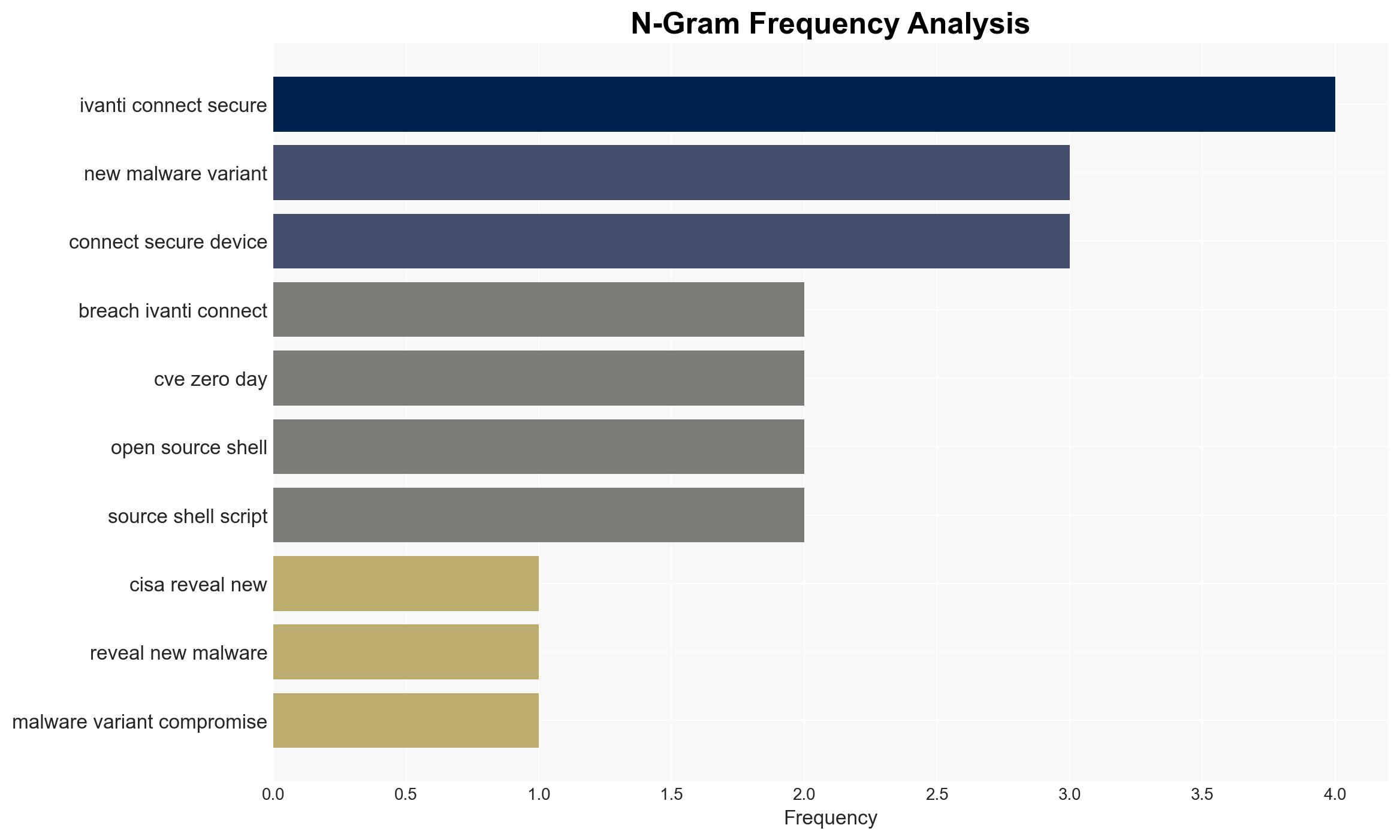
The Cybersecurity and Infrastructure Security Agency (CISA) has identified a new malware variant, named “Resurge,” targeting Ivanti Connect Secure devices. This malware exploits a zero-day vulnerability, CVE, to breach systems and maintain persistence. The attack is linked to a Chinese espionage group known as Silk Typhoon. Immediate mitigation strategies include conducting factory resets and applying updated detection signatures. Stakeholders must prioritize these actions to prevent further exploitation.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
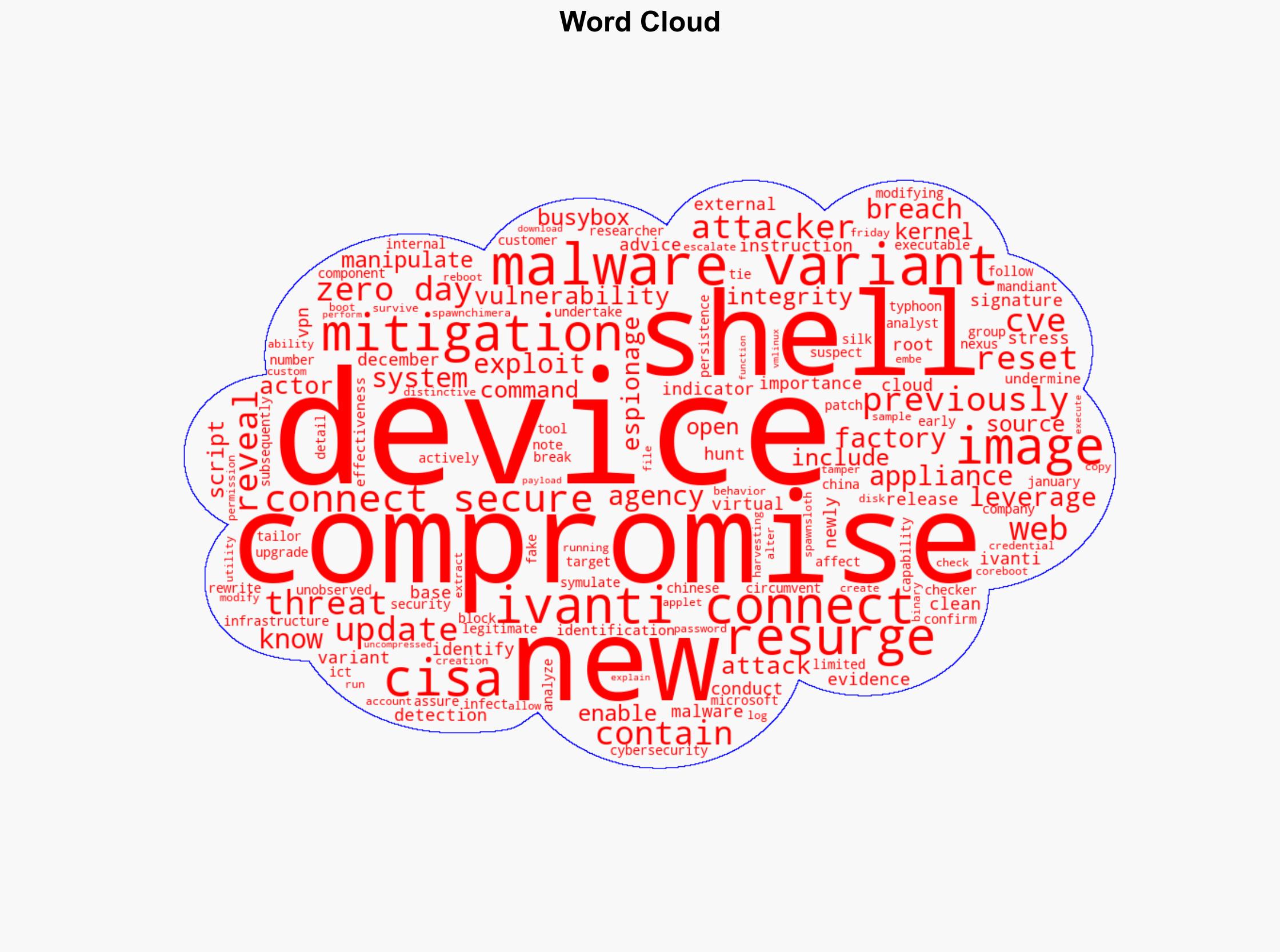
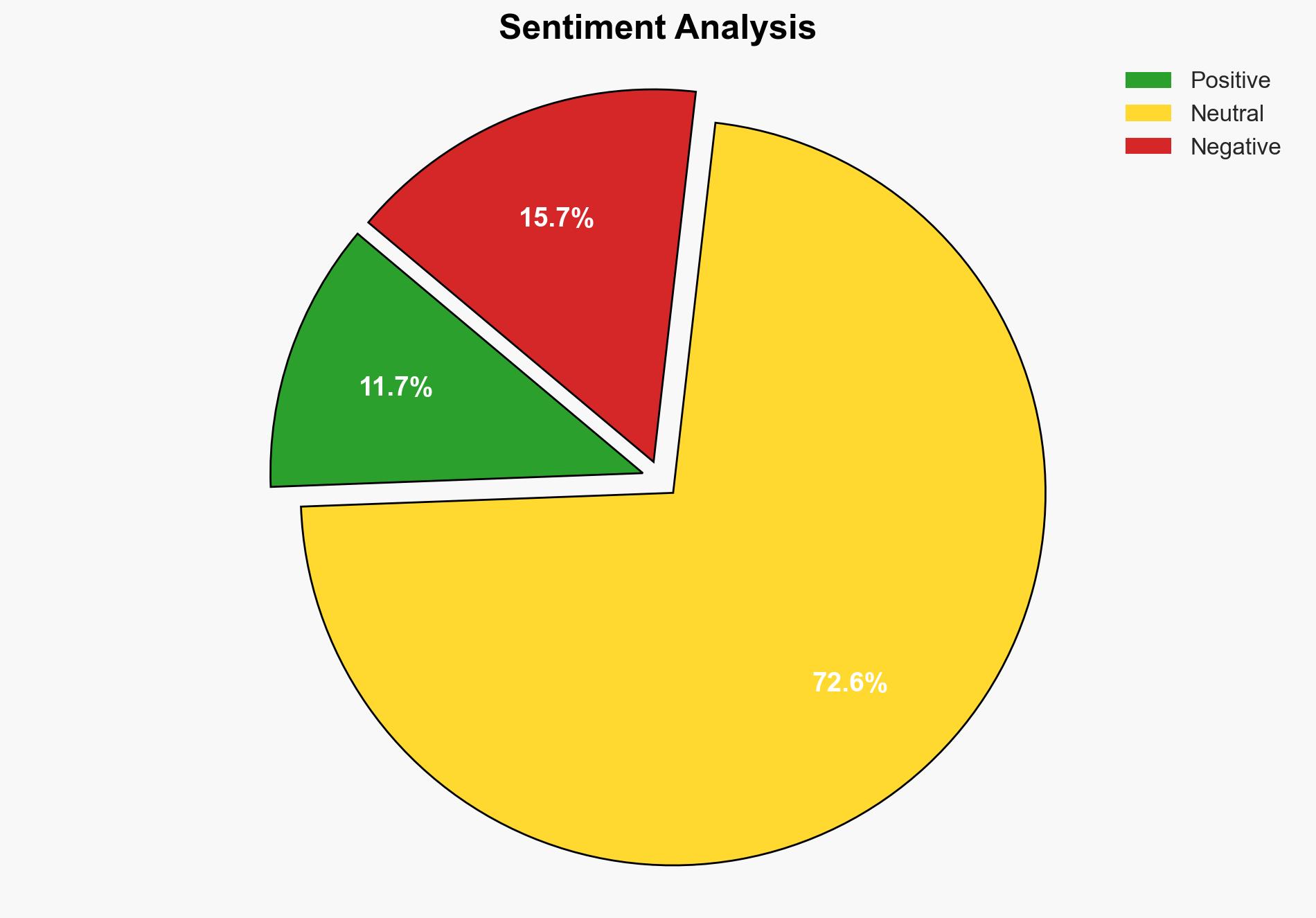
General Analysis
CISA’s disclosure highlights a sophisticated cyber threat targeting Ivanti Connect Secure VPN appliances. The Resurge malware variant is capable of surviving reboots and manipulating system integrity checks. It includes features for credential harvesting, account creation, and privilege escalation. The malware’s persistence mechanisms involve modifying core system components and deploying web shells. The attack, initially exploiting a zero-day vulnerability, underscores the evolving tactics of state-sponsored actors, particularly those with suspected ties to China.
3. Implications and Strategic Risks
The emergence of the Resurge malware variant poses significant risks to national security and economic interests. The ability of attackers to maintain persistence on compromised devices threatens the integrity of sensitive networks. This incident highlights the vulnerability of critical infrastructure to state-sponsored cyber espionage. The potential for widespread disruption and data exfiltration necessitates immediate attention from cybersecurity stakeholders.
4. Recommendations and Outlook
Recommendations:
- Conduct immediate factory resets on potentially compromised devices and apply updated detection signatures.
- Enhance monitoring for indicators of compromise and implement robust incident response protocols.
- Encourage regulatory bodies to mandate timely patch management and vulnerability disclosure.
- Invest in advanced threat detection technologies and employee cybersecurity training.
Outlook:
In the best-case scenario, swift mitigation efforts and improved cybersecurity measures will contain the threat, preventing further breaches. In the worst-case scenario, failure to address vulnerabilities could lead to extensive data breaches and operational disruptions. The most likely outcome involves ongoing attempts by state-sponsored actors to exploit similar vulnerabilities, necessitating continuous vigilance and adaptation of security strategies.
5. Key Individuals and Entities
The report mentions significant individuals and organizations involved in the analysis and response to the cyber threat. These include CISA, Ivanti, Mandiant, Microsoft, and the Silk Typhoon group. The roles and affiliations of these entities are critical to understanding the broader context of the threat landscape.